Following years of hype and anticipation, the Internet of Things has crossed over into the mainstream. With technological advancements making IoT technologies easier to implement, connected devices have become ubiquitous, and the IoT space is still growing as companies across industries seize new opportunities to benefit from IoT applications. That’s why it’s important to understand the IoT security standards and guidelines and how to leverage them.
The percentage of businesses leveraging IoT technologies has nearly doubled since 2014. From TVs, thermostats and door locks to medical sensors, fitness trackers, children’s toys and every gadget in between, a wide range of traditionally “dumb” things are becoming “smart,” and the number of smart devices in use around the globe will only continue growing as internet connectivity becomes a standard feature.
But with the growth of the IoT also comes rising concerns surrounding the security of connected devices and IoT products. These devices often contain sensitive and private information — and the threat of a massive cyberattack expands with every new device. Since connected devices can be hacked to gain access to networks, control devices and reveal sensitive personal information, data privacy and security have become a global issue. Consequently, there are a significant number of different IoT security standards and a vast amount of legislation in place to ameliorate the negative impact of the risks embedded security poses.
With IoT device security being a hot topic among manufacturers, IoT service providers, app developers and retailers, let’s take a look at the many data privacy laws, and IoT regulations and security standards centered around securing our world.
Contents
Embedded Security Privacy Laws & IoT Regulations
As the IoT grows, new regulatory frameworks are being developed and deployed with increasing frequency.
United States
Passed in December 2020, the Internet of Things Cybersecurity Improvement Act requires the National Institute of Standards and Technology (NIST) and the Office of Management and Budget (OMB) to take specified steps to increase IoT device security. The bill requires our neighbors in Boulder at NIST to develop and publish minimum IoT security standards for devices connected to information systems owned or controlled by federal government agencies, specifically around supply chain risks.
In California and Oregon, “reasonable security features” in IoT devices are now required by bills in each state. California SB 327 bans the use of preset passwords in any IoT product manufactured and sold in the state in an effort to increase password security. From wearables to home appliances to network routers, every IoT device in the Golden State must not only have a unique password to prevent hackers from malicious intrusion but also must be assigned a set of IP addresses or Bluetooth addresses.
Similar to the California law, under Oregon State HB 2395 manufacturers are required to protect connected devices and the information they store from unauthorized access, destruction, modification, use or disclosure. However, the definition in the Oregon law of “device manufacturer” is slightly different and the scope is strictly focused on home devices.
Additionally, since there are multiple types of IoT security risks — the device being hacked to gain access to networks and to control the device; and the device being hacked to gain access to sensitive personal information — the California Consumer Privacy Act of 2018 (CCPA) gives consumers more control over the personal information that businesses collect about them, securing new privacy rights for consumers, including:
- The right to know about the personal information a business collects about them and how it is used and shared;
- The right to delete personal information collected from them (with some exceptions);
- The right to opt out of the sale of their personal information; and
- The right to nondiscrimination for exercising their CCPA rights.
Under the CCPA, businesses are also required to give consumers notices explaining their privacy practices. So, even though the CCPA does not regulate commercial conduct that occurs entirely outside of California, it is rare that American businesses carry out all of their commercial activities outside of the most populous state in the country altogether.
Europe
An important component of privacy law and human rights law, the General Data Protection Regulation (GDPR) is a regulation on data protection and privacy in the European Union (EU) and the European Economic Area (EEA). The primary aim of the GDPR is to enhance individuals’ control and rights over their personal data and to simplify the regulatory environment for international business. Enforceable since May 2018, the GDPR has become a model for many other similar laws across the world, including in Argentina, Brazil, Chile, Japan, Kenya, Mauritius, South Africa, South Korea and Turkey.
Devoted to improving cyber resilience, deterrence and defense across the EU, the Cybersecurity Act of 2019 strengthens the EU Agency for cybersecurity (ENISA) and establishes a cybersecurity certification framework to ensure a common certification approach and ultimately improve cybersecurity for IoT products and services.
Japan
Way back in 2003, Japan adopted its data protection law, the Act on the Protection of Personal Information (APPI). The law applies to all business operators that handle the personal data of individuals in Japan and refers both to companies that offer goods, such as connected devices, and services in Japan. It received a major overhaul in September 2015 after a series of high-profile data breaches shook Japan, and it was amended again in 2020 to alter — and for many foreign businesses, transform — the ways in which companies conduct business in or with Japan.
In 2014, Japan’s Cybersecurity Strategy Headquarters released The Basic Act on Cybersecurity, revising it in 2016 and 2018 with regard to the development of connected devices. The act sets basic principles of cybersecurity policy, clarifies the responsibilities of the government, private entities and citizens, and stipulates a framework for cybersecurity policy and strategy.
Other Data Privacy and Security Laws and Regulations
Two new Chinese laws pertaining to embedded security and connected device data privacy came into force in the fall of 2021: the Data Security Law and the Personal Information Protection Law. The two laws provide more specificity about the data localization, data export and data protection requirements that first appeared in the Chinese Cybersecurity Law in 2017.
The Personal Data Protection Act (PDPA) in Singapore provides a baseline standard of protection for personal data, including that collected by connected devices. Comprising various requirements governing the collection, use, disclosure and care of personal data in Singapore, the PDPA recognizes both the need to protect individuals’ personal data and the need of organizations to collect, use or disclose personal data for legitimate and reasonable purposes.
One of the strictest data privacy laws in the world, South Korea’s Personal Information Protection Act (PIPA) was passed in September 2011 to protect the privacy rights of the data subject. PIPA provides very prescriptive and specific requirements — such as prior notification, opt-in consent and heavy sanctions prescribed by law — throughout the lifecycle of the handling of personal data, and its protection applies to most organizations, including government entities.
With the increasing ubiquity of connected devices, these laws play a key role in increasing trust and security in IoT products and services. Now that we’re familiar with the laws and regulations impacting data privacy and security, let’s dive into some IoT device security standard guidelines.
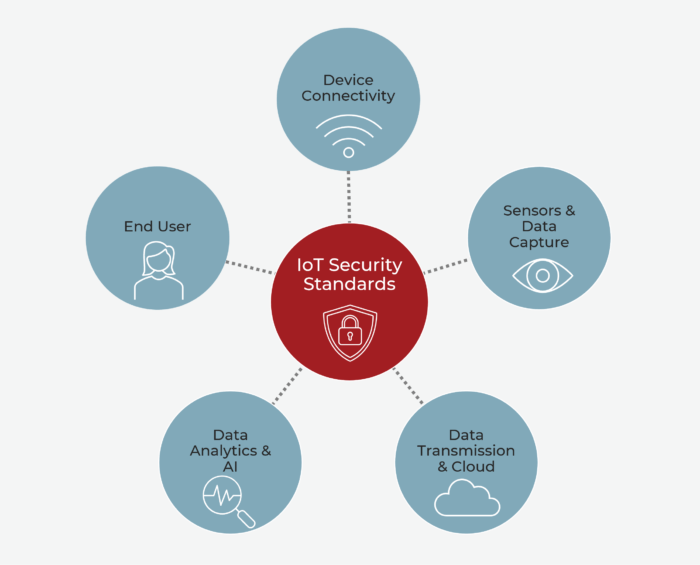
IoT Security Standards
Since IoT devices vary substantially in form and function, there isn’t a one-size-fits-all solution when it comes to embedded security for the Internet of Things. Plus, due to the global nature of the IoT market, there are myriad IoT security standards and regulations, so be sure to understand the current rules and legal requirements in your target sector.
Global
In the U.S., Canada, the U.K., Germany and France, Common Criteria (CC) is a standard for the verification of security products. Traditional IT, such as new firewalls, switches and routers, are subject to CC evaluation, and there are seven security assurance levels in total. Only recently have IoT companies begun successfully passing through the CC framework, but its stringent nature makes it one of the best available certification processes to increase the security and reliability of IoT products.
United States
Developed by NIST, the Federal Information Processing Standards regulate information technology and computer security, providing four increasing levels of security intended to cover a broad range of potential applications and environments. By specifying requirements for cryptography modules to which all government technologies must comply, the FIPS 140 series helps protect valuable data, and the new 140-3 issue will soon be implemented.
- Level 1: The lowest level of security, with no specific physical security mechanisms beyond basic requirements for production-grade components.
- Level 2: This level enhances the physical security measures of a Level 1 cryptographic module by requiring anti-tampering coating or seals as well as role-based authentication for operators to perform services.
- Level 3: Level 3 adds tamper-evident physical mechanisms and requires mechanisms that can detect and respond to attempts at intrusion, including mechanisms that zero all plaintext CSPs when an attack is detected.
- Level 4: The highest level of security includes all previous levels plus complete physical envelopment of the cryptographic module.
Part of the NIST Cybersecurity for IoT program, NISTR 8295 is a standard that adds measures for managing IoT cybersecurity and privacy risks. It is the only U.S. government-approved standard requiring connected devices to meet reasonable national security features, and it describes security/privacy activities that manufacturers should consider performing before selling their IoT devices to customers.
The UL Safety Test Institute focuses on testing materials, devices, products, equipment and buildings to prevent hazards to life and property. While UL certification is noncompulsory in the U.S. and does not include a product’s electromagnetic compatibility characteristics, certification is aimed at ensuring products attain a fair level of security and protect personal health and property safety. The UL IoT Security Rating features five security levels — Bronze, Silver, Gold, Platinum and Diamond — ranging from minimum baseline to more comprehensive security capabilities. UL’s IoT Security Rating framework aligns with prominent industry standards and can serve as a means to demonstrate conformance to those standards.
Europe
The European Telecommunications Standards Institute released in 2019 the ETSI TS 103645 standard for the cybersecurity of consumer IoT products to regulate the safety of IoT devices and related services connected to the internet. Connected device security provisions aimed at improving consumers’ privacy, digital security and safety in the standard include the following:
- Elimination of universal default passwords
- A means to manage reports of vulnerabilities
- Regular software updates
- Secure storage of credentials and security-sensitive data
- Secure communications
- Minimization of exposed attack surfaces
- Safeguards of software integrity
- Safeguards of personal data
- Resilience for system outages
- Examinations of system telemetry data
- Simplification of consumer deletion of personal data
- Simplification of installation and maintenance of devices
- Validation of input data
Released in June 2020, ETSI EN 303645 is designed to prevent large-scale, prevalent attacks against smart devices by both establishing a security baseline for connected consumer products and providing a basis for future IoT certification schemes. The first globally applicable standard for consumer IoT, ETSI EN 303645 describes building security into IoT products from the design stage and provides a set of 13 recommendations, with the top three being: no default passwords, implement a vulnerability disclosure policy and keep software updated.
With guidelines including no default passwords, implementation of a vulnerability disclosure policy, regular software updates, secure storage and communications, minimized exposure of attack surfaces, and more, the U.K.’s DCMS Code of Practice for Consumer IoT Security aims to improve the security of consumer IoT products and associated services. The code’s 13 outcome-focused guidelines highlight what is widely considered good practice in IoT device security.
Other IoT Device Security Standards Around the World
Established in September 2020, Australia’s Code of Practice: “Securing the Internet of Things for Consumers” intends to improve the security of IoT devices in Australia through a voluntary set of measures the government recommends as the minimum standard for IoT devices. Designed for an industry audience and comprising 13 principles, the Code of Practice recommends prioritization of the top three principles because action on default passwords, vulnerability disclosure and security updates will bring the largest security benefits in the short term.
Applicable to all terminal devices with a connection to the internet and telecommunications network infrastructure equipment, Brazil’s Act No. 77 establishes a set of security requirements for telecommunications equipment to minimize or correct vulnerabilities through software/firmware updates or configuration recommendations.
China’s Information Security Technology – Personal Information Security Specification (GB/T 35273-2020), while voluntary and recommended rather than mandatory, sets out best practices concerning the protection of personal information. The specification strengthens privacy protection, places more weight on the independence of will of individuals in deciding whether to share one’s PI as a condition of access to products and services and guarantees the right to consent in PI collection and usage, among other provisions. Additionally, GB/T 37344 and GB/T 35136 outline application service framework standards for wearables and smart home products, respectively.
In October 2021, India’s Department of Telecommunications released the Code of Practice for Securing Consumer Internet of Things. Based on “secure by design” principles and international best practices, the code provides baseline requirements for IoT manufacturers, service providers, mobile application developers and retailers, outlining 13 guidelines for securing consumer IoT devices.
The Telecommunications Business Act of Japan summarizes the regulatory framework for businesses in the communications sector, with amendment 34.10 stating the limited requirements for a direct IP connection. Released in November 2020 by the Connected Consumer Device Security Council (CCDS) of Japan, the IoT Common Security Requirements Guidelines 2021: CCDS-GR01-2021 is a three-level certification program for the requirements needed by common IoT devices.
Finally, in Singapore, the IMDA’s Technical Specification RG-SEC, aka Security Requirements for Residential Gateways, defines the minimum security requirements for the design and management of residential gateways to home IoT devices to protect against any security threats from the internet. By setting out to minimize the vulnerability of the individual residential gateway, the technical specification helps ensure that connected devices are better protected when purchased and deployed by consumers, thereby safeguarding both the communication networks and the devices themselves.
IoT Security Standard Wrap-Up
Some of these IoT security standards simply outline best practices, while some others will actually have some teeth if you fail to adhere to the rules. In the end, if you are planning on selling connected products in these different countries, it’s important to keep these rules in mind when designing so you don’t run afoul of any regulation. Plus, even though many of these IoT security standards are just glorified best practices, they are “best practices” for a reason. As a result, you’ll probably want to follow them so your company’s reputation isn’t tarnished by a hack.
At Cardinal Peak, we understand end-to-end security in IoT. We recognize that best security practices need to be adhered to — and they need to include means of securely updating devices in the future. From the design phase through launch and ongoing support, it’s important to design security into connected products because today’s secure devices will be vulnerable tomorrow as new vulnerabilities are found in old devices (and the libraries they use).
Whether you need help understanding the various IoT regulations and data privacy and security legislation around the globe or require connected product design and development expertise, reach out to the Cardinal Peak team today!
Uncover how Industry 4.0 technologies and IoT are reshaping entire industries in our blog post Industry 4.0 Technologies: How Connected Device Engineering Transforms Manufacturing and Supply Chains.
